Author: Jason Joerger
Most of us have heard the term “Con Man.”
“Con” is not short for convict, as many think. It’s short for confidence.
During a “Con,” the would-be perpetrator’s success in his or her nefarious endeavor is completely reliant upon gaining the confidence -or trust- of the intended victim.
Con men have been around as long as mankind. Elixir salesmen of the 19th century are iconic con men. Trust them that their elixir will cure all ailments and for a meager price the “customer” could purchase what turned out to be fish oil and turpentine.
Computer systems have given con men another means to deploy their wares.
Through the use of Social Engineering, bad actors attempt to trick victims into divulging information or taking action.
The idea behind social engineering is to take advantage of people’s natural tendencies and emotional responses, the same as it has been for Con Men throughout the millennium.
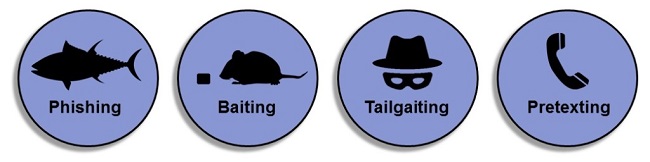
There are nine common types of social engineering today
1. Phishing
The term phishing has taken on multiple meanings, but it is generally spoofing -or faking- a legitimate address or website in hyperlink in an email, pdf or other productivity document (Word, Excel, etc.).
Many times, the email may seem to come from a trusted source.
2. Spear phishing
Spear phishing is using personal information obtained -usually through social networking platforms or publicly available information- with aim at a specific individual
3. Whaling
Whaling is phishing aimed at company executives or high-ranking government personnel
4. Vishing
Vishing is using telephone technology to pose as a reputable person/entity while attempting to extract information from the victim.
The use of Voice over IP (VoIP) systems have made vishing attacks more successful. Many VoIP software programs allow users to program in the caller ID that they wish the call recipient to see displayed.
With this software, anyone can be calling from “Wells Fargo.”
5. Baiting
Baiting involves distribution of infected physical items. “Here’s a free flash drive.”
The flash drive was free, except for the virus installed on it that took down your system or stole your information.
6. Pretexting
Pretexting is the art of establishing a scenario that makes it in the best interest to hand over private information. “Ma’am I’m calling from the Social Security Administration.
Your identity has been stolen. Please confirm your social security number, so I can begin the investigation.”
7. Watering Hole
This attack is employed by placing malicious code (virus) on a public web site commonly used by persons in a targeted category.
Scenario: I install a backdoor Trojan Horse on the Clearancejobs.com web site. The website is a job board for US Citizens with a Department of Defense clearance.
When a cleared user visits the site, the Trojan Horse opens a path to his or her system.
8. Quid Pro Quo – This for that.
Our parents told us, “If something seems too good to be true, it probably is.”
This advice has been a warning issued throughout the ages by the wise, to protect the ignorant from greed and ego.
If a Prince sends you an email saying that he’ll give you half of his $1 Billion account if you send him $100 to unlock it, there is a high likelihood that the Prince lives in his parents’ basement
9. Piggy Backing
Not the last event at the family reunion, but the act of using someone else’s authorized physical access into an area to gain unauthorized access.
You swipe your company badge on the reader to your building and another person follows you in without using his or her own badge.
The most dangerous of social engineering attacks is enabling physical access to unauthorized persons.
Unauthorized access provides a myriad of attack opportunities, including jeopardizing the safety of our people.

The number one defense against social engineering is to be defensive and guarded. Don’t trust anyone unless you are looking at them or talking to them (this isn’t a deep fake discussion).
If you don’t know someone well, do not take or provide anything that has the capability of doing you, or your interests harm. In general, require two-factor authentication before dropping your guard or providing valuable information.
As an example, I sent our Legal Department a legitimate document via email that they were not expecting, so I called them first to let them know I was sending it.
If you receive a hyperlink from your colleague, call him or her before opening it.
In addition to utilizing two-factor authentication, follow the advice of Maya Angelou, “There is an African saying which is: Be careful when a naked man offers you a shirt.”
Social engineering: The art of replacing what works with what sounds good.
— Thomas Sowell






